Eine Denial-of-Service-Attacke hat zum Ziel, den Zugriff auf einen Server oder eine Website zu verhindern. E-Banking Nutzer können von solchen Angriffen betroffen, aber auch unbewusst daran beteiligt sein. Schützen Sie sich!
Schützen Sie sich vor Denial-of-Service (DoS-) Angriffen:
- Verwenden Sie ein aktuelles Virenschutzprogramm.
- Überwachen Sie die Verbindungen mit Hilfe einer Firewall.
- Installieren Sie regelmässig Updates für Ihr Betriebssystem und alle installierten Programme.
- Passen Sie auf und seien Sie wachsam.
Es existieren verschiedene Arten von DoS-Angriffen. Die häufigste besteht im gleichzeitigen Senden von sehr grossen Datenmengen an einen Dienst auf einem Server, sodass dieser überlastet wird und auf weitere Anfragen nicht mehr antworten kann (z.B. wird die Website im Browser nicht mehr angezeigt). Dabei werden normalerweise keine Daten gestohlen oder beschädigt.
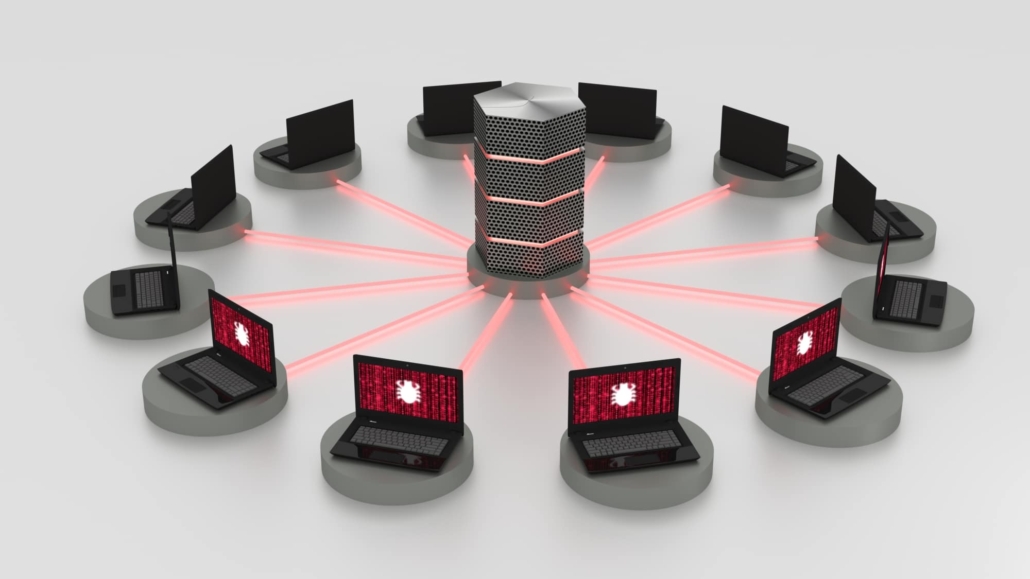
Meistens werden solch grosse Datenmengen mit Hilfe eines Botnetzes versendet. Dies wird Distributed-Denial-of-Service-Attacke (DDoS-Angriff) genannt (siehe unten).
Es ist wichtig, dass Sie sich an die «5 Schritte für Ihre digitale Sicherheit» halten, damit Ihr Gerät nicht Teil eines Botnetzes und somit zum «unfreiwilligen Beteiligten» eines DDoS-Angriffs wird.
Koordinierter Angriff von mehreren Geräten aus
(DDoS – Distributed-Denial-of-Service)
Die häufigste Art eines DoS-Angriffes ist die sogenannte Distributed-Denial-of-Service Attacke (DDoS-Angriff), welche koordiniert von einer grossen Zahl an Geräten aus durchgeführt wird.
Der DDoS-Angriff ist in zwei Schritte unterteilt. Im ersten Schritt bringt der Angreifer mehrere Geräte im Internet mittels Trojaner oder anderer Malware in seine Gewalt und baut dadurch ein sogenanntes Botnetz auf. Im zweiten Schritt übernimmt der Angreifer die Kontrolle über die infizierten Geräte (das Botnetz) und bringt diese dazu, gleichzeitig das Ziel (z. B. eine Website) anzugreifen.
Der DDoS-Angriff ist sehr effektiv, da er gleichzeitig von vielen Geräten aus erfolgt und dadurch sehr einfach die benötigte grosse Datenmenge erzeugt werden kann. Er wird vorwiegend für das Lahmlegen von Servern und Websites verwendet. Beim DDoS ist es meist schwierig, den eigentlichen Urheber des Angriffs ausfindig zu machen, da das Gerät des Angreifers das Ziel selbst nicht attackiert.